
PKI & CMP - Why Secure Systems Don't Scale Without Automated Certificate Management
Security Doesn't Start with TLS
Security is a central cornerstone of modern systems. Furthermore, the Cyber Resilience Act (CRA) mandates various security measures. Especially in distributed systems connected to an IT infrastructure, requirements must be implemented cleanly and consistently from the very beginning. In practice, terms like certificates, TLS, and secure connections are frequently mentioned. What is often overlooked: without proper certificate management, security quickly becomes an operational risk.
Particularly in distributed, highly automated systems, the question is not whether certificates are used, but how they are managed throughout their entire lifecycle.
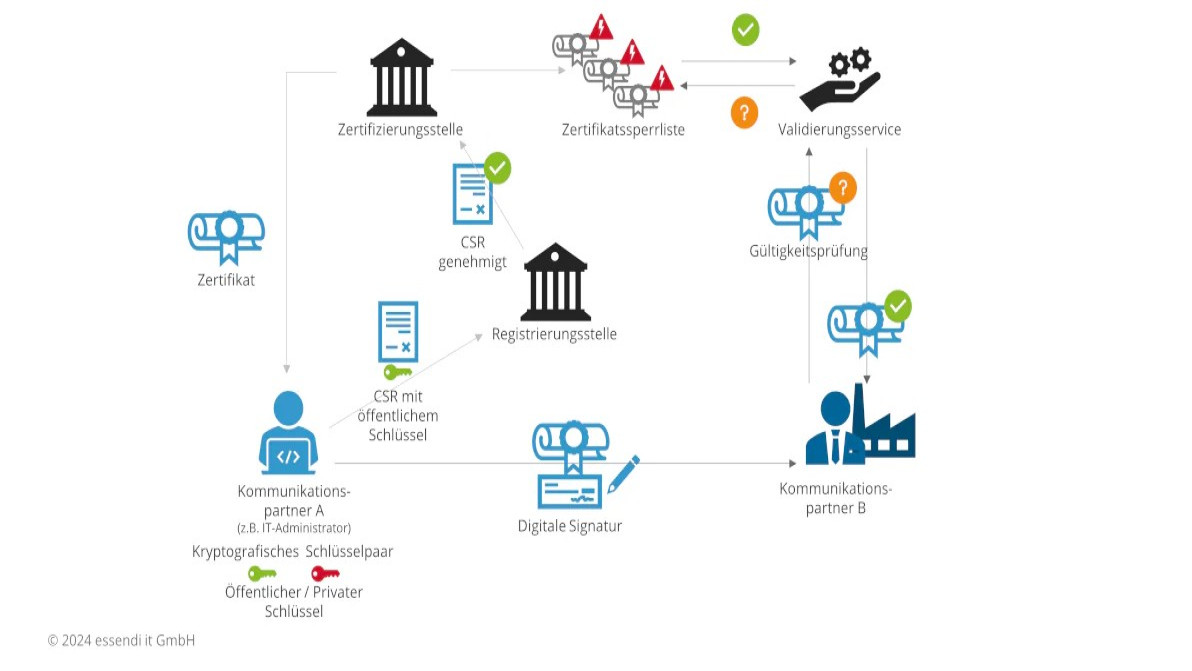
PKI – More Than Just a Certificate Authority
A Public Key Infrastructure (PKI) forms the basis for digital identities based on asymmetric cryptography. In industrial or operational environments, these are usually not public CAs, but private or organization-internal PKIs with clearly defined trust anchors.
A PKI ensures that:
- Identities are uniquely verifiable
- Certificates can be signed, renewed, and revoked
- Trust is built in a scalable and traceable manner
A PKI does not just consist of a CA, but of several logically separated components:
- CA (Certification Authority) – signs certificates
- RA (Registration Authority) – verifies identities and requests
- CRL / OCSP – provides revocation information (Certificate Revocation List and validation service)
This separation is a proven architectural principle to ensure security, traceability, and scalability.
Source: https://www.essendi.ch/was_ist_eine_pki/
Why Manual Certificate Processes No Longer Work and What the Solution Is
In many projects—though not ours—reality still looks like this:
- Certificates are created manually
- Expirations are forgotten or chosen very generously
- Revocations are incomplete or inconsistently documented
Even if these processes seem manageable at first glance, they are rarely executed consistently when done manually and lead to:
- Security gaps due to unrevoked and compromised certificates
- Operational interruptions caused by invalid certificates
- High administrative effort and high risk due to countless manual steps
For a single system with few certificates, this might still be barely manageable. At the latest, with several parallel systems, many endpoints, long lifespans, or high availability requirements, it becomes clear: certificate management must be automated.
This is exactly where the Certificate Management Protocol (CMP) comes in.
CMP is a standardized protocol for mapping the entire certificate lifecycle, including:
- Initial certificate request (IR / CR)
- Renewal of existing certificates (KUR)
- Suspension and revocation (RR)
A key advantage: The client generates its own key pair. As a result, the private key never leaves the system.
Furthermore, CMP defines clear mechanisms for authenticating certificate requests, for example via pre-provisioned secrets or existing trust anchors, making it particularly suitable for corporate and industrial PKIs.
In contrast to web-centric protocols like ACME, CMP is designed for long-lived systems, device fleets, and controlled trust domains.
Our Experience with PKI & CMP
Security holds a high priority in all our projects. As a representative example, a test system in the railway sector can be mentioned. In this project, CMP was used to:
- Automatically obtain certificates from an existing PKI
- Distribute these securely to existing applications
- Secure TLS-based connections (e.g., OPC-UA, NTS)
PKI & CMP are part of a dedicated security partition, which bundles several security-critical services and forms the basis for a consistent trust architecture.
Conclusion
- PKI is the foundation of secure communication
- CMP makes this foundation operational, automatable, and scalable
- Modern IT security is hardly feasible without automated certificate management
In a future blog post, we will show why even time in distributed systems is no longer trustworthy without PKI and what role certificates play in secured time synchronization.

Nicolas Andres
BSc HES-SO in Systems Engineering
Embedded Software Engineer
Über den Autor
Nicolas Andres has been working as an embedded software engineer at CSA Engineering AG for six years, focusing on the development of firmware in C and C++.
For a test system in the railway environment, he played a key role in integrating CMP into an existing PKI, gaining practical experience in the automated certificate management of security-critical systems.
